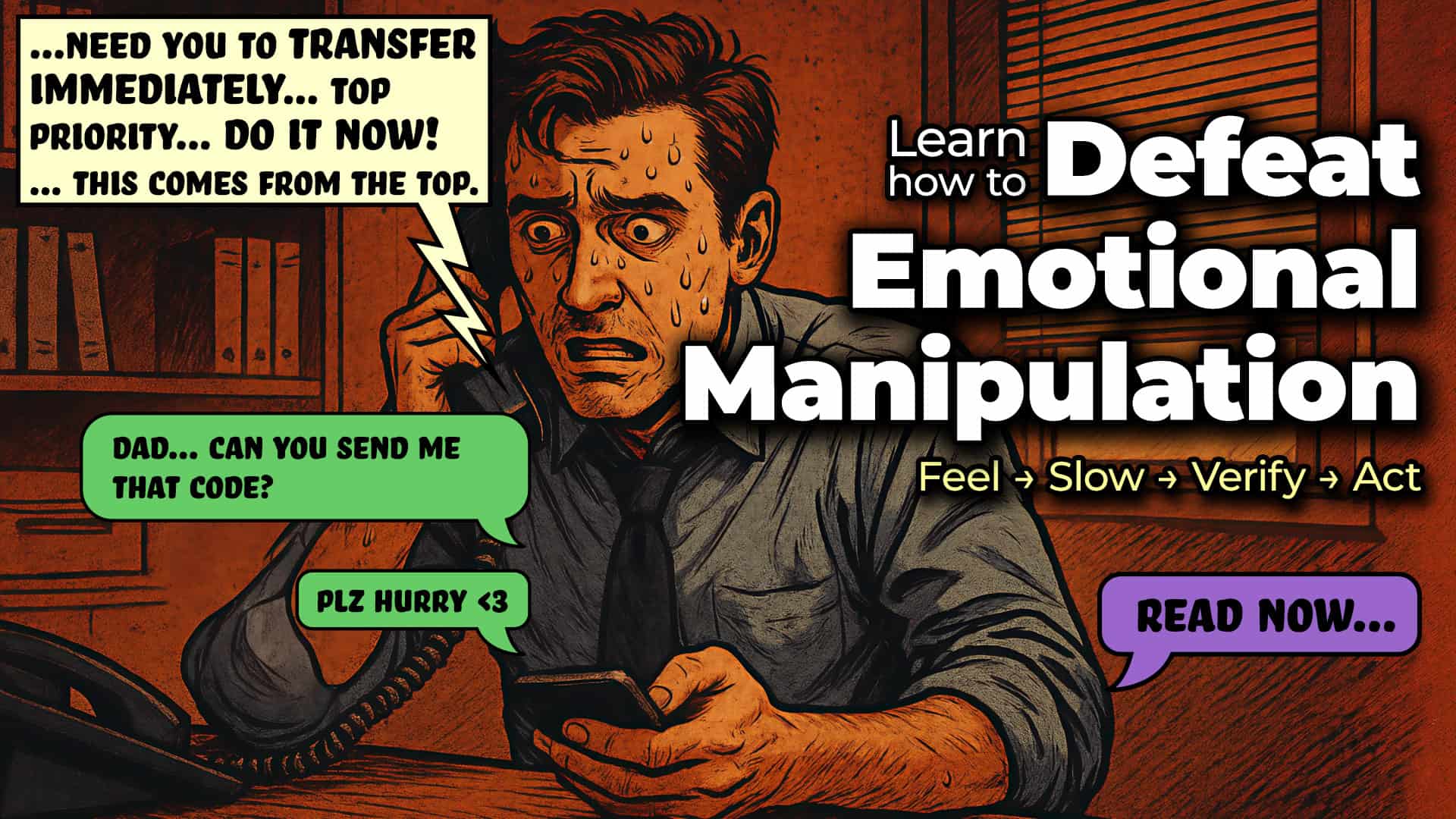
Your phone rings. It sounds exactly like your CFO, your CEO, or a family member in distress. They’re panicked and need you to act immediately—to transfer money, reset a password, or run a “quick fix” command. Before you know it, your heart is racing and you’re about to comply.
This is emotional manipulation in action. Attackers don’t need to break your systems when they can hijack your decision‑making.
In 2026, social engineering attacks are faster and more convincing than ever. AI voice cloning, deepfakes, and hyper‑personalized lures have pushed voice phishing (vishing) past email as the top method attackers use to gain initial access to systems and accounts. Even people who consider themselves security‑aware are falling for these scams. The consequences are severe: millions of dollars lost, sensitive data exposed, and long‑term damage to trust and reputation.
The good news? You don’t need to be a cybersecurity expert to fight back. You just need a simple, memorable framework that works every time:
Feel → Slow → Verify → Act
This four‑step mental model is designed for everyone—from teenagers and grandparents to executives and frontline employees. It takes less than 60 seconds to apply, and it can stop an attack before it starts.
Why Emotional Manipulation Works So Well
Here’s the uncomfortable truth: attackers don’t need to be hackers in hoodies typing furiously at a keyboard. The most effective cybercriminals today are psychologists with laptops.
They understand how the human brain responds to stress, fear, urgency, and authority—and they weaponize it.
When your brain perceives an urgent threat, it shifts into survival mode. Complex reasoning shuts down. You stop thinking and start reacting. That’s exactly what attackers are counting on.
Before 2020, most social engineering attacks arrived by email. Phishing links and fake login pages gave people time to pause, think, and verify. Phone calls and text messages changed everything. They create immediate pressure, a sense of personal connection, and a demand for instant action.
Now, with AI tools widely available, attackers can:
- Clone a CEO’s voice from seconds of audio
- Generate perfectly personalized messages using data scraped from LinkedIn
- Coordinate email + SMS + phone calls within minutes
Why Modern Attacks Are So Effective
Urgency & Fear
Attackers create artificial deadlines—“Act now or your account will be locked”—triggering panic that overrides rational thought.
Authority Bias
We’re wired to obey authority. Calls that sound like a CEO, bank employee, or government agent exploit this instinct automatically.
AI‑Powered Impersonation
Voice cloning, deepfakes, and hyper‑personalized lures are now accessible to almost anyone.
Multi‑Channel Attacks
When email, text, and phone calls all reference the same issue, the situation feels legitimate—even when it isn’t.
The result is sobering. Even security‑aware professionals still fall for these attacks when they’re sufficiently urgent and personalized. That’s why a simple, repeatable framework like Feel → Slow → Verify → Act is so powerful: it gives you a structured response when your emotions are screaming at you to act.
The Framework at a Glance
Feel → Slow → Verify → Act is a four‑step mental model designed to interrupt the emotional hijack attackers rely on.
It works for:
- Phone calls
- SMS and messaging apps
- Emails
- Video calls
- In‑person requests
The entire process can take as little as 30–60 seconds—but that pause is often the difference between staying safe and becoming a victim.
Each step builds on the one before it:
- Recognize your emotional state
- Create space to think
- Independently confirm the request
- Take informed action
Skipping a step—especially Slow or Verify—is exactly what attackers hope you’ll do.
Legitimate people and organizations will always respect verification. Anyone who pressures you not to verify is revealing themselves.
Step 1 of 4: FEEL — Recognize the Emotional Trigger
Attackers don’t just want your money or passwords—they want your reaction.
The first step is noticing what’s happening inside you. When you can name the emotion, you begin to take control again.
Common Emotional Triggers
- Urgency — “This has to happen right now”
- Fear — “Your account will be shut down”
- Authority — “This request is from the CEO”
- Guilt — “I thought I could trust you”
- Helpfulness — “I just need your help for a minute”
- Confusion — “Let me walk you through this quickly”
Red Flags in Modern Attacks
- Unexpected requests for money, passwords, or MFA codes
- Threats of immediate consequences
- Spoofed caller IDs showing familiar numbers
- Overly personal details scraped from social media
- Pressure to stay on the same call or channel
- Requests to keep secrets from colleagues or family
Pro tip: Say the emotion out loud:
“I feel rushed right now.”
That alone can reactivate rational thinking.
Attackers also use positive emotions—excitement, relief, or good news. If a message makes you feel anything strongly, that’s your cue to pause.
Step 2 of 4: SLOW — Create Deliberate Space
Urgency is the attacker’s most powerful weapon.
If you feel like you have to act right now, you’re already under attack.
How to Slow Down
On a Phone Call
Say calmly:
“I need a moment to think this through. I’ll call you back.”
Then hang up.
Texts & Emails
Put the device down. Step away for 60 seconds. Take three deep breaths.
Business Requests
Adopt a hard rule: no financial, credential, or access changes on the same call they’re requested.
Slowing down isn’t rude—it’s professional. Legitimate requests can wait. Malicious ones can’t.
Step 3 of 4: VERIFY — Confirm Through an Independent Channel
This is where most attacks fail.
Attackers can clone voices and spoof numbers—but they can’t control real, trusted communication channels.
Best Verification Practices
- Call back using a number you already trust
- Use official apps or internal systems
- Never use contact details provided in the suspicious message
- Require dual approval for high‑risk actions
- Involve a second person whenever possible
Simple Verification Script
“Hi, I received a request about [topic]. I’m calling you back on our standard number to confirm. Can you repeat the request?”
If the real person doesn’t know what you’re talking about, you’ve just stopped an attack.
If you can’t reach them? Don’t act. Waiting is a security feature.
Step 4 of 4: ACT — Respond Safely and Report
Once verified, take the correct action—through proper channels and without rushing.
If Legitimate
Follow normal procedures. Document everything. Keep safeguards in place.
If Suspicious
Stop engaging. Don’t click, reply, or explain. Report it immediately.
How to Report
- SMS: Forward to 7726 (US carriers)
- Work: Use your company’s security or IT reporting channel
- Document: Record the details and take screenshots
- Warn Others: Attackers often target multiple people at once
Reporting helps protect everyone—not just you.
Real‑World Attacks This Framework Stops
- Deepfake CEO Wire Transfer
- IT Help Desk MFA Reset Scam
- Grandchild Emergency Impersonation
- ClickFix Command Malware Attack
Every one of these relied on speed, emotion, and unverified trust. A single pause and callback would have stopped them.
Making the Framework Stick
For Individuals & Families
- Teach all four steps to everyone
- Create a family verification phrase
- Agree: no money moves without a callback
- Practice with role‑play scenarios
For Businesses & Teams
- Require out‑of‑band verification
- Eliminate same‑channel approvals
- Run realistic vishing simulations
- Reward reporting—not silence
Your Strongest Defense Is a Calm, Skeptical Human
In the AI era, technology alone isn’t enough. Firewalls can’t stop a convincing voice on the phone.
Your strongest defense is a human who refuses to act on emotion alone.
Feel → Slow → Verify → Act is a mental reset button.
It’s fast. It’s free. And it works against today’s attacks—and tomorrow’s.
The next time an urgent request hits your phone, remember four words:
Feel. Slow. Verify. Act.
That pause is your superpower.
Humans are our biggest vulnerability. Test and Train your organization with Alias Social Engineering Testing.