
Security Leadership: What Separates Security Practitioners from Security Leadership? (Part 2)
Note: The Following is the second part of a series on CISO/Security Leadership. Click here for Part One: CISO Soft ...

Note: The Following is the second part of a series on CISO/Security Leadership. Click here for Part One: CISO Soft ...

When people think of a Chief Information Security Officer (CISO), they often picture someone deeply technical — an expert in ...
FOR IMMEDIATE RELEASE Alias Cybersecurity Selected to Compete in Prestigious Vishing Competition at DEFCON 33 Oklahoma City, OK – May ...

When it comes to protecting your business, not all service providers are created equal. It’s common for companies to lean ...

How to Stay Safe Online from Phishing Scams – 2025 Edition! Alright, listen up, you beautiful nerds! Phishing scams in ...
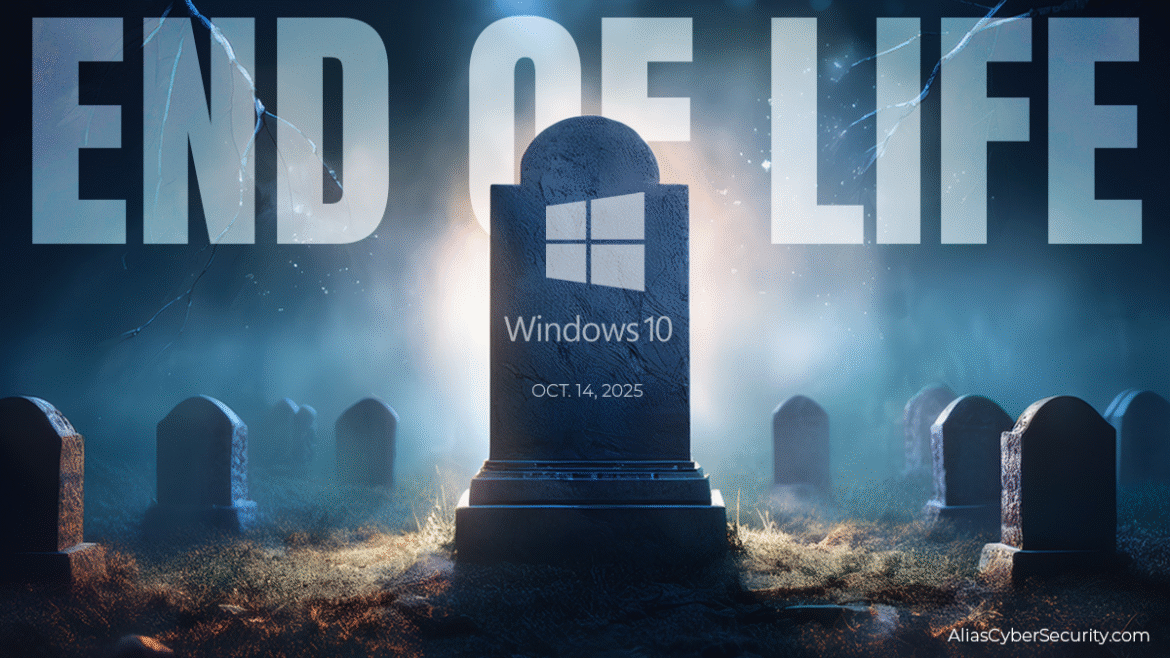
Tick… Tick… Tick…That ominous sound you hear isn’t just your imagination—it’s the countdown to October 14, 2025, the day Microsoft officially ...

Microsoft’s Majorana 1 Chip: A Quantum Leap Forward or Cybersecurity Nightmare? The unveiling of a new quantum computing chip has ...
As US cybersecurity professionals, we are well-versed in the tactics, techniques, and procedures (TTPs) of advanced persistent threats (APTs) from ...
In recent years, there has been an alarming growth in the number of data breaches affecting 500 or more individuals, ...