
Why Time Is One of the Hardest Problems in Digital Forensics
In digital forensics, time is not just metadata—it is evidence. Nearly every action performed by a user or system leaves behind artifacts tied to a timestamp, and those timestamps form ...
Blog Will Arnett todayApril 7, 2026
Modern geopolitical conflict has increasingly expanded beyond traditional battlefields – with cyber operations becoming a critical complement to conventional military force.
Modern conflict is no longer confined to physical terrain. Over the last decade, cyber operations targeting critical infrastructure have moved from a theoretical risk to an accepted component of statecraft and military strategy. This reality has become especially visible during the current conflict involving Iran, where cyber operations are widely assessed as a likely escalation vector from all parties involved due to their deniability, speed, and reach.
In early 2026, open-source reporting and government advisories confirmed that following U.S. military strikes against Iranian nuclear and military capabilities, the risk of retaliatory cyber activity against U.S. and allied critical infrastructure systems increased significantly. Multiple U.S. agencies—including CISA, the FBI, NSA, and DoD—issued formal warnings urging critical infrastructure operators to harden defenses against nation-state and proxy cyber actors aligned with Iran.
With a stated deadline falling on the date that I write this (Tuesday, April 7, 2026), President Donald Trump has underscored the stakes of the confrontation by explicitly warning that energy and utility systems could be targeted in any escalation with Iran—signaling a clear recognition that critical infrastructure, including power, water, and transportation networks, now sits squarely in the strategic crosshairs of modern warfare.
This is not political posturing—it is strategic reality. For cybersecurity engineers and security leaders, this moment underscores a hard truth: critical infrastructure cyber attacks are no longer a hypothetical risk. They are an assumed capability of modern adversaries.
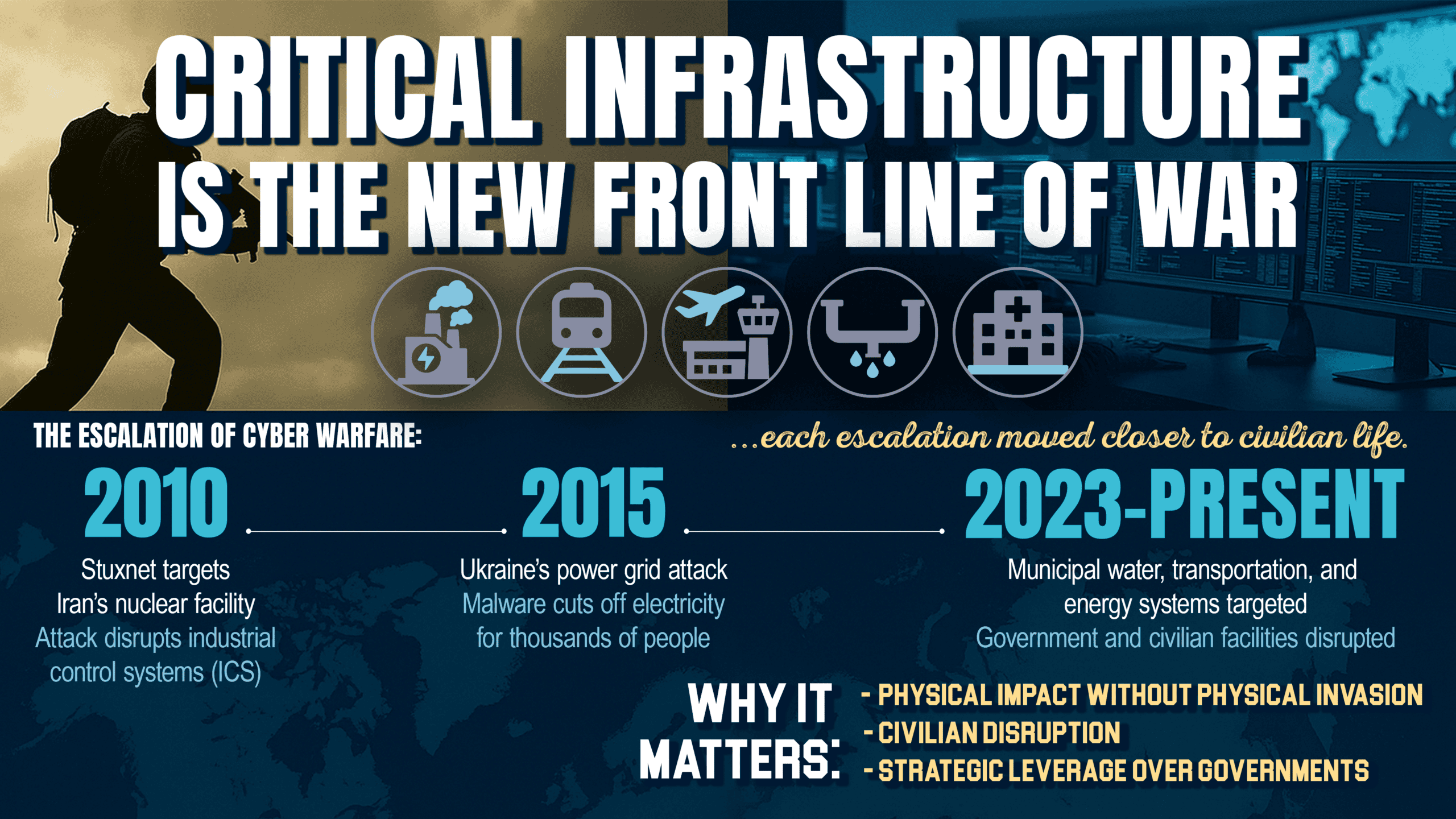
Cyber warfare targeting IT and OT systems has evolved steadily since the early 2000s. Several prominent nation-state incidents illustrate how infrastructure-centric cyber attacks became normalized tools of conflict.
1. Stuxnet – The First Digital Weapon (U.S. & Israel vs. Iran)
Discovered in 2010, Stuxnet is widely regarded as the first true cyber weapon. Designed to target Siemens PLCs controlling Iranian uranium enrichment centrifuges, the malware manipulated physical processes while falsifying sensor data to operators. This attack demonstrated that cyber operations could cause real-world physical damage without a single missile being launched.
Stuxnet fundamentally changed how nation-states viewed industrial control systems (ICS) and SCADA environments—transforming them from operational assets into strategic vulnerabilities.
2. Russia’s Cyber Attacks on Ukraine’s Power Grid (2015–Present)
Beginning in 2015 and escalating after 2022, Russian threat actors repeatedly disrupted Ukraine’s electrical grid using malware such as BlackEnergy, Industroyer, and Industroyer2. These operations combined IT intrusion techniques with deep OT knowledge, exploiting substation automation and protective relays to cause widespread blackouts.
Unlike Stuxnet’s covert precision, these attacks were intentionally disruptive—designed to degrade civilian morale, overwhelm emergency response, and create cascading societal impact.
3. Iranian Cyber Operations Against Water and Municipal Systems (2023–2026)
Iranian state-aligned actors have increasingly targeted undersecured U.S. and allied infrastructure, particularly municipal water systems, healthcare networks, and transportation environments. Joint advisories confirm attempted and successful intrusions into PLCs, remote access systems, and internet-facing OT devices, often using default credentials or unpatched firmware.
These examples reinforce a consistent pattern: critical infrastructure cyber attacks are asymmetric, deniable, and disproportionately impactful.
When most people hear “critical infrastructure,” they think of power plants and water utilities. While those are vital, the true attack surface is much broader—and often poorly understood.
Well-Known Targets:
Often Overlooked or Underappreciated Assets:
Attackers do not need to “take down the grid” to create chaos. Disrupting a single wastewater facility, airport baggage system, or traffic control network can ripple through emergency services, commerce, and public trust.
From an adversary’s perspective, critical infrastructure is the perfect cyber target.
Infrastructure systems are expensive to build but relatively inexpensive to disrupt. A small exploit—misconfigured VPN, exposed HMI, or vulnerable PLC—can have outsized consequences.
Many ICS environments were engineered decades ago for reliability and uptime—not security. Legacy protocols (Modbus, DNP3, BACnet) lack authentication and encryption, making them ideal targets once network access is gained.
Even minor disruptions compel rapid response. Governments must act quickly when water, power, or transportation is affected—often before full attribution or containment is possible.
Infrastructure attacks directly affect civilians. Blackouts, water shortages, grounded flights, or halted manufacturing generate fear, uncertainty, and loss of public confidence—objectives aligned with psychological operations and influence campaigns.Threat intelligence reporting consistently emphasizes that nation-state actors exploit targets of opportunity—especially organizations with limited staffing, aging infrastructure, and hybrid IT/OT environments.
As global conflicts increasingly play out through attacks on critical infrastructure, the impacts are felt not on distant battlefields but in local communities. Municipalities and local governments now find themselves on the front lines, facing constrained budgets, legacy systems, and regulatory complexity—yet resilience is still within reach through a disciplined, focused approach.
You cannot protect what you cannot see. Maintaining an accurate inventory of IT, OT, and IIoT assets—especially internet-facing components—is foundational.
Strict network segmentation, unidirectional gateways, and minimal trust boundaries significantly reduce blast radius during an intrusion.
Most infrastructure breaches begin at the edge:
Traditional SOC tools rarely understand ICS traffic. OT-aware monitoring enables detection of abnormal commands, logic changes, and unsafe process states.
Municipal systems must plan not only for ransomware—but for process manipulation, safety events, and prolonged outages. Practicing coordinated IT/OT incident response is essential.
Few local governments can staff 24/7 OT security expertise internally. Managed detection, threat intelligence, and digital forensics partnerships are force multipliers—especially during geopolitical crises.
The era of cyber war is not coming—it is already here. Critical infrastructure cyber attacks represent one of the most serious, complex, and existential risks facing municipalities, transportation authorities, and industrial organizations today.
From Iranian-aligned operations against water utilities to nation-state attacks on power grids and manufacturing environments, the message is clear: critical infrastructure is now frontline terrain.
That is why organizations responsible for public safety and essential services need partners who understand both IT and OT realities, who speak the language of engineers, and who have proven experience defending environments where downtime is not an option.
Alias Cybersecurity & Digital Forensics has earned a trusted reputation securing IT/OT systems for municipalities and local governments, transportation and logistics organizations (including airports), and manufacturing facilities. Our Red Team penetration testers and our SOC of Blue Team threat monitors combine deep technical expertise, real-world incident response experience, and a clear understanding of how modern cyber warfare targets critical infrastructure.
If your organization is responsible for systems that people depend on every day, now is the time to reassess assumptions, strengthen defenses, and prepare for the threats that define modern conflict—not tomorrow’s.
The cyber war room is already active. Make sure your infrastructure is ready.
Written by: Will Arnett
Tagged as: cyber warfare, critical infrastructure, IT/OT, iran, russia, ukraine, cyber attacks.

Blog Andrew Peters
In digital forensics, time is not just metadata—it is evidence. Nearly every action performed by a user or system leaves behind artifacts tied to a timestamp, and those timestamps form ...




Copyright 2019 Cyber Security Design Concept by <a href="http://qantumthemes.com?rel=demo" target="_blank">QantumThemes</a>.